Unlocking the Power of Tor: The Ultimate Guide to Online Anonymity
The dark web has long been shrouded in mystery, with many people assuming it's a haven for malicious activities. However, the truth is that the Tor network, also known as The Onion Router, is a powerful tool for online anonymity that has been used by legitimate users for decades. In this article, we'll delve into the world of Tor, exploring its history, technology, benefits, and best practices for using it safely and effectively.
Tor was first developed in the 1990s by a team of cryptographers and computer scientists at the Naval Research Laboratory, with the goal of creating a secure and private communication network for the US military. The project was later open-sourced and became the foundation for the open-source browser software that we know today. Today, Tor is used by individuals, organizations, and governments around the world to protect their online identity, access censored information, and maintain digital freedom.
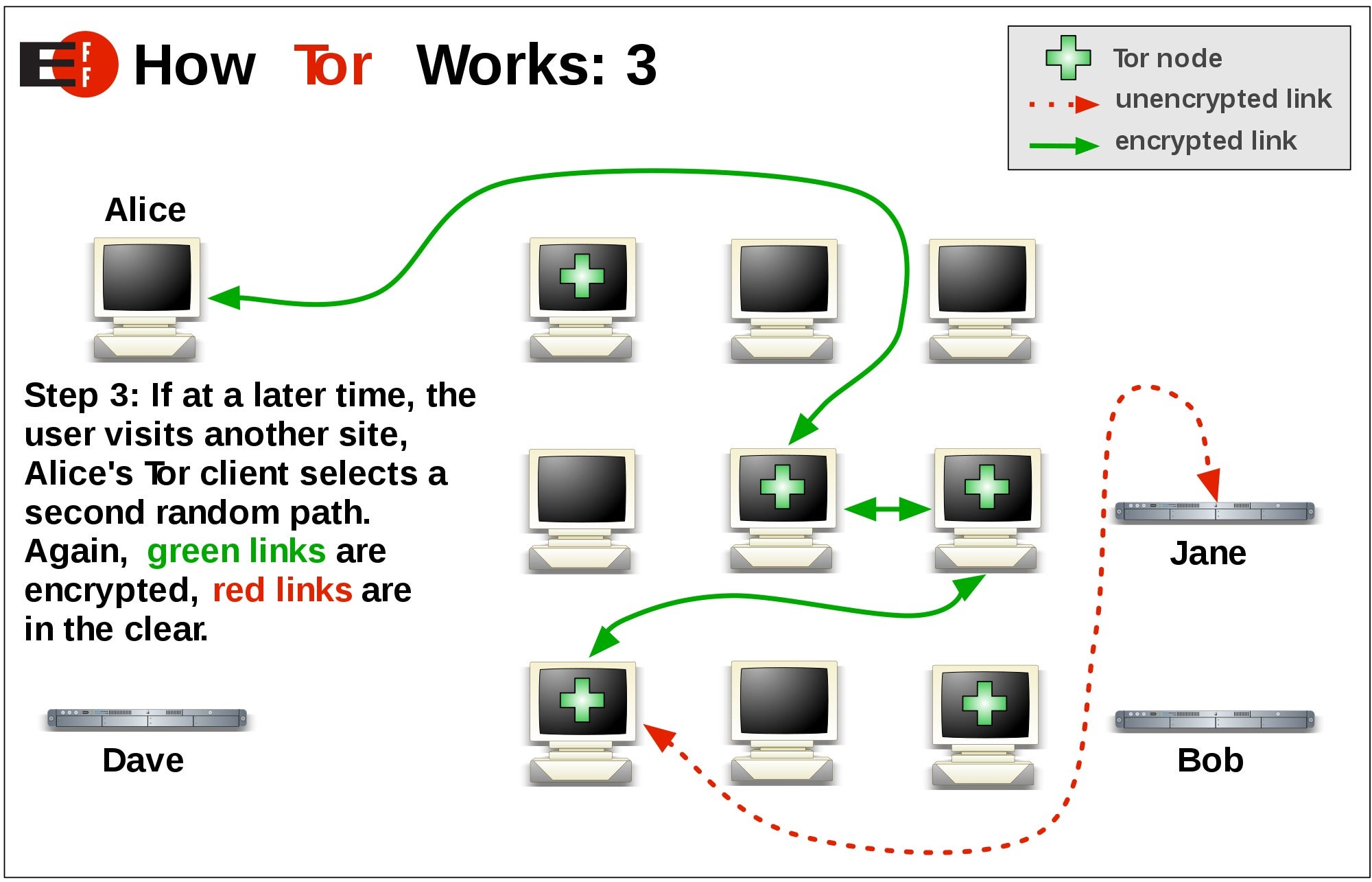
Tor's key innovation is its use of a distributed network of volunteer-run servers to encrypt and anonymize internet traffic. Here's how it works:
- When you access the Tor network, your internet traffic is routed through multiple nodes, or relays, in a process called tunneling.
- Each relay adds a layer of encryption and anonymity, making it difficult to track the origin and destination of your traffic.
- The final relay forwards your traffic to its intended destination, without revealing your IP address or any other identifying information.
Tor's technology has many benefits, including:
• Enhanced online security: Tor encrypts your internet traffic, making it difficult for hackers and surveillance agencies to intercept and eavesdrop on your communication.
• Anonymity: Tor masks your IP address, making it difficult for anyone to track your online activity or identify you as a specific user.
• Access to censored content: Tor allows you to access websites and online resources that are blocked in certain countries or regions due to censorship.
• Digital freedom: Tor provides users with the ability to communicate freely and anonymously, without fear of reprisal or surveillance.
Understanding Tor's Security Features
Tor's security features are designed to protect your online identity and communication. Here are some key features:
- Encryption: Tor uses advanced encryption protocols, such as PGP and SSL/TLS, to secure your internet traffic.
- Onion routing: Tor's tunneling system uses onion routing to encrypt and anonymize your traffic.
- Relay network: Tor's network of volunteer-run relays provides an additional layer of security and anonymity.
To get the most out of Tor, it's essential to understand its security features and best practices. Here are some tips:
• Use a reputable Tor browser: Download and install a reputable Tor browser, such as Tor Browser or Tails, to ensure you have the latest security patches and features.
• Keep your software up-to-date: Regularly update your Tor browser and any other software you use to ensure you have the latest security patches and features.
• Use strong passwords: Use strong, unique passwords for all of your online accounts to protect yourself from unauthorized access.
• Avoid using Tor for illegal activities: While Tor is designed for anonymity, it's essential to use it responsibly and avoid engaging in illegal activities.
Exploring the Dark Web with Tor
The dark web is often associated with illicit activities, but it's also a platform for legitimate users to access censored information and online resources. Here are some key facts about the dark web:
- Definition: The dark web is a part of the internet that is not indexed by search engines and is often accessed through Tor.
- Content: The dark web contains a wide range of content, including online forums, marketplaces, and archives of censored information.
- Access: To access the dark web, you need to use a Tor browser and navigate to the.onion domain of the website you want to visit.
Some popular dark web destinations include:
• The Hidden Wiki: A directory of dark web websites and resources.
• Silk Road: A marketplace for buying and selling goods and services.
• DuckDuckGo: A search engine that indexes the dark web.
Tor vs. VPN: What's the Difference?
When it comes to online anonymity, both Tor and VPNs are popular options. However, they work in different ways and have different benefits. Here's a comparison of Tor and VPNs:
- Tor: Tor encrypts and anonymizes internet traffic, making it difficult to track your online activity or identify you as a specific user.
- VPN: VPNs create a secure, encrypted connection between your device and a VPN server, masking your IP address and location.
- Benefits: Tor provides anonymity, while VPNs provide security and location masking.
When to use each:
• Tor: Use Tor for accessing censored information, online forums, and marketplaces, as well as for anonymous browsing.
• VPN: Use a VPN for secure browsing, accessing geo-restricted content, and protecting your data from hackers and surveillance agencies.
Using Tor Safely and Effectively
To get the most out of Tor, it's essential to use it safely and effectively. Here are some best practices:
- Use a reputable Tor browser: Download and install a reputable Tor browser, such as Tor Browser or Tails, to ensure you have the latest security patches and features.
- Keep your software up-to-date: Regularly update your Tor browser and any other software you use to ensure you have the latest security patches and features.
- Use strong passwords: Use strong, unique passwords for all of your online accounts to protect yourself from unauthorized access.
- Avoid using Tor for illegal activities: While Tor is designed for anonymity, it's essential to use it responsibly and avoid engaging in illegal activities.
By following these
Recent Post
Unlocking The Secrets Of Menopause: Expert Insights On Navigating Life After 40 With Paolo Tantoco
Tensions Rise As Trump Officials Defend Tariffs Amid Market Volatility And Warnings For Savers And Retirees
Rosie O'Donnell Teases Trump Move, Posts Disruptive Selfie From Abroad
Wings For The Win: Capitals Edge Ducks 7-4 In Thrilling Matchup
Ducks Fall Short: Key Takeaways From Thrilling 7-4 Loss To Capitals
Article Recommendations
- Unveiling The Enchanting World Of Sophie Rain: A Literary Journey Into The Heart Of Nature
- Patrick Fugit: A Talented Actor With A Diverse Career
- Justin Bieber's Journey: From Heartthrob To Icon