Encrypting Webcams: A Ransomware Tactic That Can Bypass Endpoint Detection and Response
The world of cybersecurity is constantly evolving, with new threats emerging every day. One of the most insidious and effective tactics used by ransomware attackers is encrypting webcams. This tactic allows attackers to gain access to a victim's sensitive information, including personal data, financial information, and more, without even being physically present. In this article, we will explore the tactics used by ransomware attackers to encrypt webcams, and how this can bypass endpoint detection and response (EDR) systems.
Ransomware attacks have become increasingly common in recent years, with many organizations and individuals falling victim to these attacks. One of the reasons why ransomware attacks are so effective is because they often exploit human psychology. Many people are hesitant to report a ransomware attack to their IT department, fearing that they will be ridiculed or that their business will be shut down. However, this fear can be exploited by attackers, who may use the threat of a ransomware attack to scare victims into paying the ransom without reporting the attack to anyone.
Encrypting webcams is a tactic that is often used by ransomware attackers to gain access to a victim's sensitive information. When a victim's webcam is encrypted, the attacker gains access to the victim's computer and can use the webcam to access the victim's sensitive information. This can include personal data, financial information, and more. The attacker can also use the webcam to access the victim's surroundings, allowing them to gather information about the victim's location and activities.
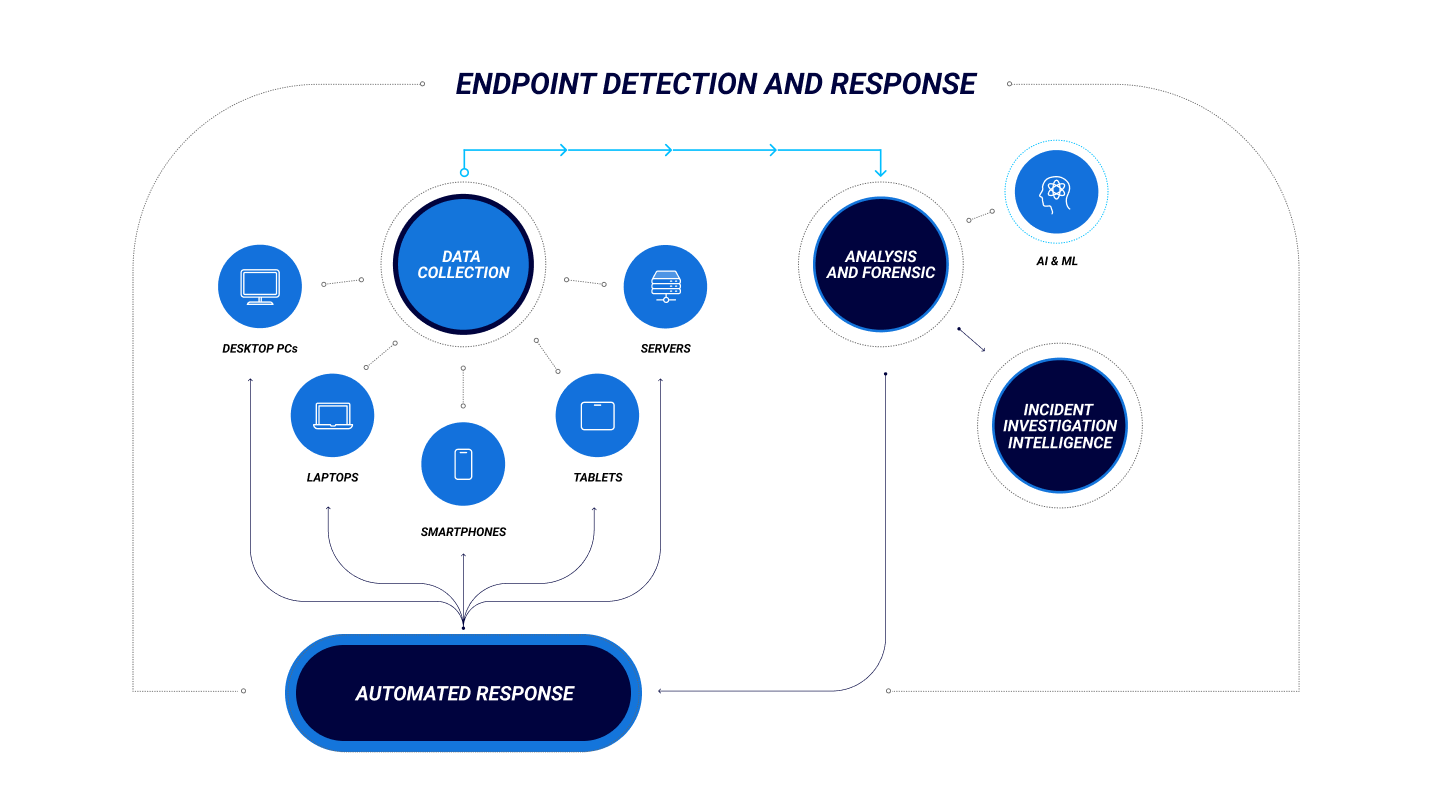
Endpoint detection and response (EDR) systems are designed to detect and respond to endpoint threats, including ransomware attacks. However, encrypting webcams can bypass EDR systems, making it difficult for them to detect and respond to these types of attacks. This is because EDR systems are often designed to detect specific types of malware, rather than cryptographically sensitive data.
How Encrypting Webcams Works
Encrypting webcams is a complex process that requires a deep understanding of cybersecurity threats and tactics. Here's a step-by-step guide on how encrypting webcams works:
- The attacker sends a phishing email or instant message to the victim, containing a malicious link or attachment.
- The victim clicks on the link or opens the attachment, which downloads malware to their computer.
- The malware encrypts the victim's webcam, using a strong encryption algorithm to protect the data.
- The attacker gains access to the victim's computer and can use the webcam to access the victim's sensitive information.
- The attacker can also use the webcam to access the victim's surroundings, allowing them to gather information about the victim's location and activities.
Types of Ransomware That Encrypt Webcams
There are several types of ransomware that are designed to encrypt webcams. Some of the most common types of ransomware that encrypt webcams include:
- Doxware: Doxware is a type of ransomware that encrypts files and demands a ransom in exchange for the decryption key. However, some versions of doxware also encrypt webcams, allowing attackers to access the victim's sensitive information.
- Ransomware-as-a-Service (RaaS): RaaS is a type of ransomware that is designed to be easy to use and distribute. Many RaaS platforms include tools for encrypting webcams, making it easy for attackers to gain access to sensitive information.
- File-Ransomware: File-ransomware is a type of ransomware that encrypts files and demands a ransom in exchange for the decryption key. However, some versions of file-ransomware also encrypt webcams, allowing attackers to access the victim's sensitive information.
Common Signs of Webcam Encryption
It can be difficult to determine if a ransomware attack has encrypted a webcam. However, there are several common signs that may indicate that a ransomware attack has occurred:
- Unusual network activity: If the victim's computer is experiencing unusual network activity, such as rapid file transfers or strange connection attempts, it may be a sign that a ransomware attack has occurred.
- Malware files: If the victim's computer has a large number of malware files, it may be a sign that a ransomware attack has occurred.
- Unusual system behavior: If the victim's computer is behaving unusually, such as freezing or crashing frequently, it may be a sign that a ransomware attack has occurred.
- Email notifications: If the victim receives an email notification from the attacker, it may be a sign that a ransomware attack has occurred.
How to Protect Yourself from Webcam Encryption
Protecting yourself from webcam encryption requires a combination of technical and non-technical measures. Here are some steps you can take to protect yourself:
- Use antivirus software: Installing antivirus software can help protect your computer from malware, including ransomware.
- Use a firewall: Installing a firewall can help block unauthorized access to your computer and network.
- Use strong passwords: Using strong passwords can help prevent attackers from gaining access to your computer and sensitive information.
- Be cautious with emails: Being cautious with emails and avoiding suspicious links or attachments can help prevent phishing attacks.
- Regularly back up data: Regularly backing up data can help ensure that you can recover your data in case of a ransomware attack.
Technical Measures
Here are some technical measures you can take to protect yourself from webcam encryption:
- Use a VPN: Using a VPN can help encrypt your internet connection and prevent attackers from accessing your sensitive information.
- Use a browser extension: Using a browser extension, such as a password manager or a security tool, can help protect your computer from malware and phishing attacks.
- Use a network intrusion detection system (NIDS): Using a N
Recent Post
Unlocking The Secrets Of Menopause: Expert Insights On Navigating Life After 40 With Paolo Tantoco
Tensions Rise As Trump Officials Defend Tariffs Amid Market Volatility And Warnings For Savers And Retirees
Rosie O'Donnell Teases Trump Move, Posts Disruptive Selfie From Abroad
Wings For The Win: Capitals Edge Ducks 7-4 In Thrilling Matchup
Ducks Fall Short: Key Takeaways From Thrilling 7-4 Loss To Capitals
Article Recommendations
- Unveiling The Enigmatic Charm Of Mara Corday: From Hollywood Starlet To Mysterious Icon
- Unveiling The Hidden Meaning Of "Whenid Piddyie": A Tale Of Secret Communication
- Unveiling The True Weight: Sabrina Carpenter's Physique Revealed