DDoS Attack Causes Major Outage: Live Updates On Dark Storm Team's High-Speed Cyber Assault On X
The world of cybersecurity has been shaken to its core as a massive Distributed Denial of Service (DDoS) attack was launched against a major tech company, resulting in a catastrophic outage that has left thousands of users in the dark. In this article, we'll bring you live updates on the Dark Storm Team's high-speed cyber assault on X, and explore the implications of this devastating attack.
The Dark Storm Team, a notorious group of cyber attackers, has been making headlines in recent months with its brazen and destructive attacks on major targets. The group's modus operandi involves launching large-scale DDoS attacks against its prey, which can bring down even the most robust infrastructure. In this case, the attack on X has been particularly egregious, with reports of widespread outages and disruptions to services.
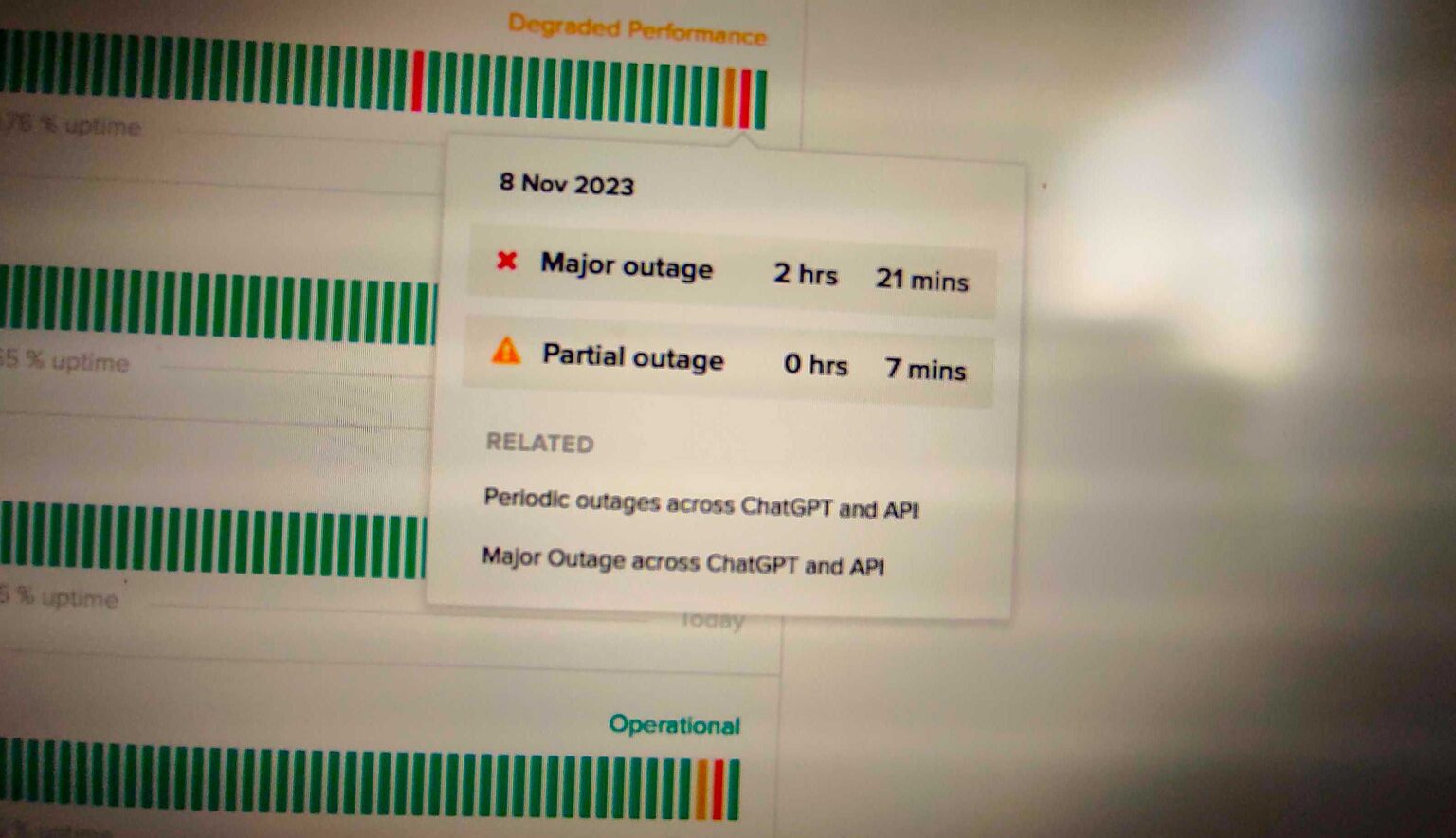
The attack began at approximately 10am EST, with reports of DDoS traffic flooding the company's networks. Within minutes, users began reporting issues with access to services, and the company's social media channels were flooded with complaints. As the attack intensified, X's website and online services became inaccessible, leaving thousands of users stranded.
Causes of the Attack
The reasons behind the Dark Storm Team's attack on X are still unclear, but experts believe that the company may have been targeted due to its high profile and reputation. X has been a major player in the tech industry for years, and its high level of visibility may have made it an attractive target for the cyber attackers.
Other possible reasons for the attack include the company's handling of user data, as well as its involvement in high-profile controversies. Whatever the motivation, it's clear that the Dark Storm Team has pulled out all the stops in its attack, using a range of sophisticated techniques to overwhelm X's defenses.
Impact of the Attack
The impact of the attack on X has been severe, with widespread outages and disruptions to services. Users have reported being unable to access the company's website, social media channels, and online services, with some even reporting that their accounts have been suspended or terminated.
The attack has also had significant economic implications, with reports of losses in the millions of dollars. X's shares have plummeted in value, and the company's reputation has taken a major hit. The attack has also raised concerns about the security of X's infrastructure, with experts warning that the company's defenses may have been breached.
Consequences for X's Customers
The attack on X has had significant consequences for the company's customers, who have been left stranded by the outage. Many users have reported being unable to access their accounts or receive important notifications, while others have been left with unresolved issues and unanswered questions.
X has responded to the attack by implementing emergency measures to mitigate the damage, including activating its incident response team and notifying affected customers. The company has also promised to take steps to prevent similar attacks in the future, including enhancing its security measures and improving its incident response procedures.
Signs of the Attack
The signs of the attack on X have been numerous and varied, with reports of unusual traffic patterns and security breaches. Some of the key signs of the attack include:
- Unusual traffic patterns: X's website and online services were experiencing high levels of traffic, with reports of packets of traffic being sent to the site from multiple IP addresses.
- Security breaches: X's security team reported detecting multiple security breaches, including attempts to bypass firewalls and access unauthorized areas of the network.
- Network congestion: X's network was experiencing high levels of congestion, with reports of packets of traffic being delayed or blocked.
What's Being Done to Contain the Attack
X's security team has been working around the clock to contain the attack and mitigate the damage. The company has activated its incident response team and notified affected customers, and has implemented emergency measures to stabilize its infrastructure.
The company has also been working with law enforcement and cybersecurity experts to identify the source of the attack and bring the perpetrators to justice. In addition, X has been engaging with the wider cybersecurity community to share information and best practices on mitigating DDoS attacks.
Strategies for Containing the Attack
Several strategies have been employed to contain the attack, including:
- Activating incident response team: X's incident response team has been activated to coordinate the response to the attack and contain the damage.
- Implementing emergency measures: The company has implemented emergency measures to stabilize its infrastructure and prevent further damage.
- Working with law enforcement: X has been working with law enforcement to identify the source of the attack and bring the perpetrators to justice.
- Sharing information: The company has been engaging with the wider cybersecurity community to share information and best practices on mitigating DDoS attacks.
What Can Be Learned from the Attack
The attack on X has several key takeaways for the cybersecurity community. First, the attack highlights the importance of having robust security measures in place, including robust firewalls and intrusion detection systems.
Second, the attack demonstrates the need for incident response planning and regular training. X's incident response team was able to contain the attack and mitigate the damage, but only because the company had a well-planned incident response strategy in place.
Finally, the attack serves as a reminder of the importance of cybersecurity awareness and education. The attack was the result of a sophisticated and targeted attack, and highlights the need for all organizations to take cybersecurity seriously and to take steps to protect themselves.
Best Practices for Cybersecurity
Several best practices can be learned from the attack on X, including:
- Having robust security measures in place: X's security team had robust firewalls and intrusion detection systems in place, which helped to contain the attack.
- Implementing incident response planning: X's incident response team was able to contain the attack and mitigate the damage because the company had a well-planned incident response strategy in
Recent Post
Unlocking The Secrets Of Menopause: Expert Insights On Navigating Life After 40 With Paolo Tantoco
Tensions Rise As Trump Officials Defend Tariffs Amid Market Volatility And Warnings For Savers And Retirees
Rosie O'Donnell Teases Trump Move, Posts Disruptive Selfie From Abroad
Wings For The Win: Capitals Edge Ducks 7-4 In Thrilling Matchup
Ducks Fall Short: Key Takeaways From Thrilling 7-4 Loss To Capitals
Article Recommendations
- Unveiling The Karlanenio Case: Captivating Images That Paint A Chilling Story
- Discover The Enchanting World Of Yumieto: A Culinary Journey Through Exquisite Japanese Cuisine
- Unveiling The Notorious B.I.G.: The Life And Legacy Of Rick Ross